Addressing cyber threats in any organization remains critical. Threats such as ransomware, phishing, and Trojans have become highly sophisticated, and it’s impossible to think of a perfect IT environment. These threats cause massive losses to businesses and individuals alike. According to the Washington Post, an estimated $1 trillion was lost to cybercrime in 2020 with many other surprising cybersecurity trends.
With cyber threats on a steady rise, organizations have had to rethink their IT security approaches and strategies. Approaches such as the CMMC help cushion organizations from various cyber threats.
Navigating the certification process can be overwhelming- though it does not necessarily need to be! With this in mind, we’ll take a closer look at components that contribute to CMMC and specifically identify how pentesting fits into the certification process.
With that in mind, read on to understand the CMMC framework and how it works! (Explore more cybersecurity frameworks)
What is Cybersecurity Maturity Model Certification?
The Cybersecurity Maturity Model Certification (CMMC) is a security framework by the US Department of Defense (DoD) to assess its contractors and subcontractors' security, capability, and resilience. This framework aims to eliminate vulnerabilities in the supply chain and improve security practices. Ideally, created to cushion the US defense department from intellectual property breaches that could weaken its operations.
The CMMC is built on four elements: control practices, security domains, process, and capabilities. A combination of these elements creates risk-proof protection for DoD. The DoD partners with numerous subcontractors who possess its information.
With government software development, a slight breach can lead to massive leakage of sensitive data, which could be detrimental to the country’s overall security. Since different contractors have access to information tiers, the DoD created the CMMC with a tiered approach. Contractors have to meet specific security testing requirements depending on the prospective contracts.
CMMC Certification Levels: Requirements of each Level
The CMMC framework takes a 5-tier approach. Level 1 is the most basic, while level 5 is the most advanced maturity level. The DoD defines the levels required by a contractor depending on the data managed in the contract. To achieve certification for each level, you must attain specific requirements through the collaboration of different cybersecurity components.
Here are the relevant practices, requirements, and processes for each level.
Level 1: Basic Cyber Hygiene
This level involves 17 different security controls. Organizations must perform basic cybersecurity practices such as antivirus, strong passwords and multi-factor authentication, and secure Wi-Fi connections. It also requires employees to protect Federal Contract Information (FCI) for information meant to remain private.
Level 2: Intermediate Cyber Hygiene
CMMC level 2 certification requires organizations to document intermediate cyber hygiene practices to protect any Controlled Unclassified Information (CUI). This is done through implementing the National Institute of Standards and Technology’s (NIST) Special Publication 800-171 (NIST 800-171 r2) requirements.
The NIST 800-171 provides the requirements for protecting the confidentiality of information. To achieve the certification level, you must implement the provisions of this special publication.
Level 3: Good Cyber Hygiene
On top of the NIST 800-171 r2, a company should have a management plan to implement quality cyber hygiene to safeguard CUI. It requires an organization to create and maintain a plan that demonstrates its institutional approach to data and information protection. To pass level 3 certification, your company should demonstrate the implementation of various practices such as spam protection, DNS filtering, the ability to backup and restore data, real-time monitoring, and regular risk assessments.
Level 4: Proactive
For your company to achieve level 4 certification, it should have proactive techniques and strategies to respond to Advanced Persistent Threats (APTs). Companies need a preemptive and substantial cybersecurity program for CUI protection. Any potential contractor or subcontractor should proactively review and measure the effectiveness of its techniques and strategies for data protection.
It’s at this level and beyond that requirements compel companies to pentest their systems for existing vulnerabilities. The specific requirements focus on both manual pentesting programs and automated scanning solutions.
Level 5: Advanced/Progressive
This is the most advanced security model certification level. It requires organizations to implement a mechanism that ensures their security practices are proactively optimized. Level 5 certified organizations must have a proactive and advanced cybersecurity approach. Companies must ensure the protection of CUI from APTs, but with more sophistication and depth.
To comply, a company should understand what exactly is required. The five cybersecurity maturity levels are an essential factor in protecting sensitive information from IT risks and cyberattacks.
Who Needs the CMMC?
If you are a DoD contractor, CMMC certification is mandatory. This IT security framework applies to all contractors and subcontractors dealing directly with the DoD, who works with over 300,000 contractors and subcontractors.
Most contractors need up to level 3 certification for federal contract eligibility. These organizations include small businesses, supply chains, foreign suppliers, and manufacturers that supply items to the DoD. Any contractor willing to do business with the DoD must at least meet the basic CMMC requirements.
The certification level depends on the company’s access to CUI. Contractors that possess FCI but do not possess CUI require level 1 certification. Prime contractors with sensitive CUI require at least level 4 certification. They are highly targeted by cybercriminals and must have robust IT security strategies in place.
Sub-tier suppliers sub-contracted by the prime companies also need to ensure they are compliant with the relevant cybersecurity maturity levels. They are required to obtain their certification to prove compliance with the set IT security standards.
How do You Get a Cybersecurity Maturity Model Certification?
The DoD offers licensed assessors to help perform cybersecurity audits to organizations. The exact level you need to be certified to be awarded a contract is stated in the Request for Proposal (RFP).
Companies can be certified by third-party assessors (C3PAO). The assessors provide schedule assessments, evaluate security strengths and weaknesses, and determine if the company needs requirements for prospective cybersecurity maturity levels. In case there are issues, companies are given up to 90 days to resolve them.
Why is this Important?
The DoD has over 300,000 subcontractors in its database. With contracts exceeding $402 billion, the DoD has to implement stringent IT security measures. This helps prevent detrimental cyberattacks that could lead to the loss of crucial information that may compromise overall security. The DoD rolled out this security framework to facilitate a “defense in depth” strategy across its contractor base.
Start a Pentest for Compliance in your organization today. CMMC certification is essential if you want to do business with the DoD. If you are aiming at certain contracts, it’s essential to seek cybersecurity certification.
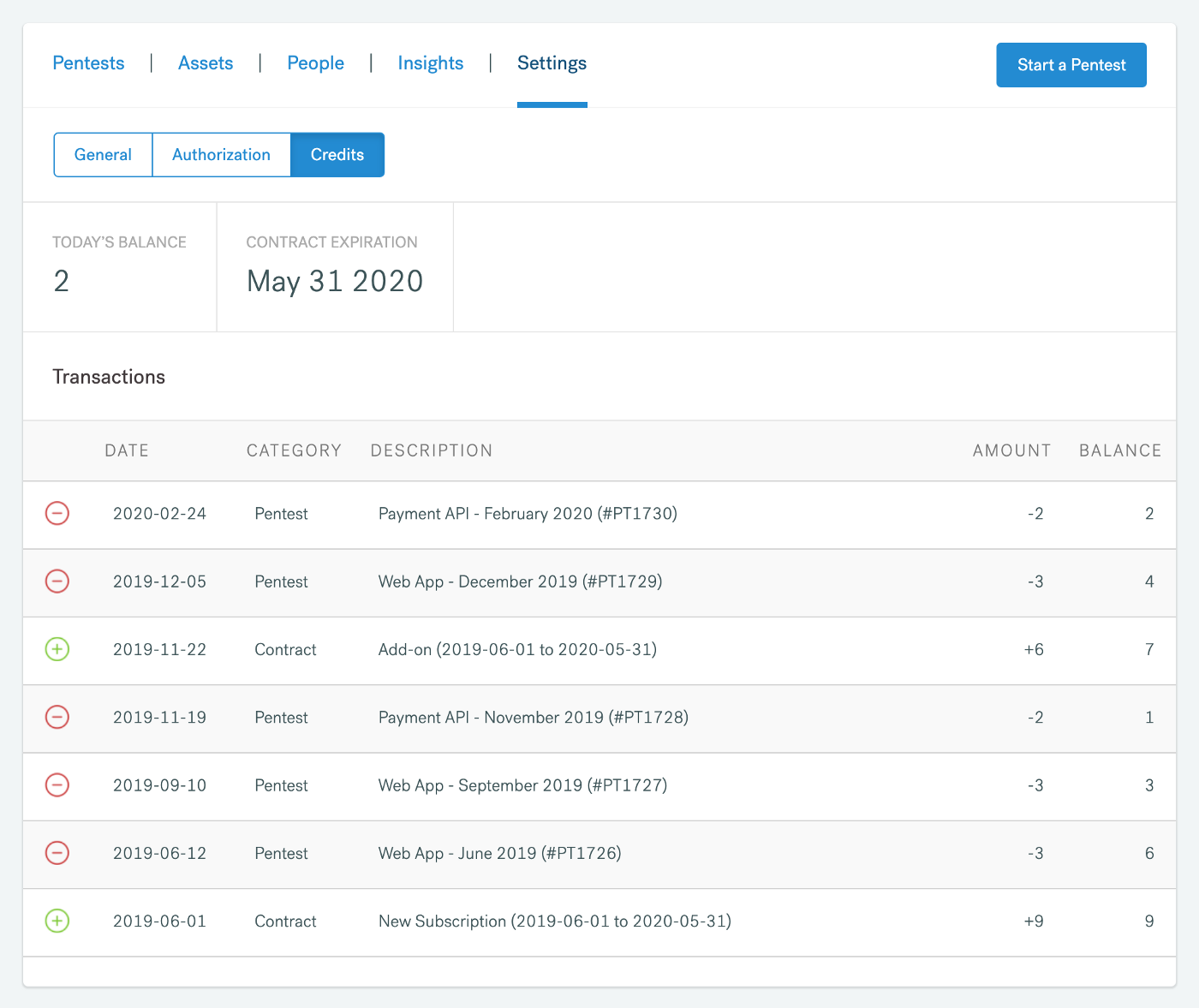
For levels 4 and 5 of certification, Cobalt Penetration-as-a-Service simplifies your pentesting compliance requirements. We offer a seamless platform, where you can start a brand new pentest in as little as 24 hours. Contact Cobalt today to see how we can improve your pentesting requirements faster and more efficiently for CMMC certification.