Bug bounty programs are becoming an increasingly popular method of finding security bugs on the internet. Google, Facebook and Paypal are just some of the companies who now run such programs. But when and how did the idea for this cost-effective, crowdsourced security testing model arise? In this post, I look a little deeper into the interesting history of bug bounty programs.
My initial research was based on an excellent presentation by Michael Coates, ”Bug bounty programs for the web”; an equally great article by David J. Maloney, “Bug bounties: It is a matter of business risk“; and the presentation “Follow the Money: Security Researchers, Disclosure, Confidence and Profit,” by Jake Kouns and Carsten Eiram. Based on these sources, I’ve drawn up this annotated bug bounty program timeline.
1995 — Netscape launches first bug bounty program
On October 10th, 1995, Netscape launched the very first bug bounty program, which offered cash rewards to those who were able to find security bugs in their Netscape Navigator 2.0 Beta. Matt Horner, Netscape’s Vice President of marketing, explained at the time: “By rewarding users for quickly identifying and reporting bugs back to us, this program will encourage an extensive, open review of Netscape Navigator 2.0 and will help us to continue to create products of the highest quality.” Netscape’s first-mover mentality was impressive, but the idea did not catch on with other software vendors. The company’s bug bounty program continued until the final release of Netscape Navigator 2.0 where the winners were announced.
2002 — IDefense — Middleman for bug bounties
As Netscape’s bug bounty methodology did not catch on to other vendors, the security company IDefense, who were later bought by Verisign, began an initiative in 2002. Their vulnerability contributor program offered researchers cash rewards of up to $400 for reporting vulnerabilities in software to them. IDefense would then act as a middleman between the researcher and the software vendors.
2004 — Mozilla Firefox Bug bounty
In the summer of 2004, nine years after the Netscape bug bounty, the Mozilla foundation launched a bug bounty program offering rewards of $500 for researchers able to identify critical vulnerabilities in Firefox. The program was sponsored by entrepreneur (and space tourist) Mark Shuttleworth and the Linux distributor Linspire. The Mozilla bug bounty program is still going strong today, expanded to cover most of Mozilla’s products.
2005 — Zero Day Initiative
In 2005, IDefense competitor TippingPoint launched another “middleman” program, called the Zero Day Initiative (ZDI). Just like IDefense, TippingPoint connected the security community with the vendors, by offering cash rewards for reports on vulnerabilities. The ZDI is still running, now by Hewlett-Packard, who acquired TippingPoint’s parent company 3Com in 2010. David Endler, who has worked for both IDefense and TippingPoint and been a prime mover behind both of their programs, has written a nice blog post, “Remembering five years of vulnerability markets,” describing the period from 2002 to the launch of ZDI.
2007 — Pwn2Own
Three weeks before 2007 CanSecWest conference, Dragos Ruiu announced the PWN2OWN contest, a hunt for security bugs in Macs OSX. This was Ruiu’s way of showing frustration with the way Apple handled security and disclosure. The contest was held within a limited time frame, with the prize initially announced as a laptop, but later upgraded to $10,000 reward provided by ZDI. PWN2OWNwas a great success and has become a recurring event at CanSecWest. In 2014, $850,000 was paid out in rewards to skilled researchers. This contest-style bug bounty model has also recently been used by Stripe, in their capture the flag contest.

2010 — Google kickstarts bug bounties for web applications
In 2010, the vulnerability reward program for Google web properties really kickstarted the trend towards bug bounty programs for web applications. Earlier the same year, Google had launched a similar program for the open-source Chromium project, with good success. Google’s reward program, that openly invited researchers worldwide, was similar to the one Mozilla launched in 2004. This year a lot happened on the bug bounty scene: Mozilla decided to expand their program to web applications, Baracuda networks launched a bug bounty, and Deutsche Post, the German federal postal service, launched a bug bounty on their secure messaging service.
2011 — Facebook whitehat program
Facebook followed in the footsteps of Google and launched their whitehat program in 2011. Facebook would pay out minimum rewards of $500, with no upper limit. The Facebook whitehat program is still running today, and more than $2M has been paid out in rewards, including $1.5M in 2013 alone.
Today — Higher rewards, internet bug bounty and bug bounty as-a-service
Online businesses of all sizes, inspired by companies such as Google and Facebook, today feature ongoing bug bounty programs to secure web applications and avoid the business costs of cybercrime. Even Microsoft now runs a bug bounty offering $100,000 in rewards for the discovery of critical vulnerabilities. Reward sizes have increased with the popularity and legitimacy of these programs: Google’s rewards, for instance, are five times greater today than in 2010.
But the story of bug bounties is still in its early chapters. Last year, Microsoft and Facebook joined forces to sponsor the Internet Bug Bounty, a program dedicated finding vulnerabilities in frameworks, such as Ruby on Rails or Django, that are used by many applications. Google likewise extended their own program to a number of open source projects.
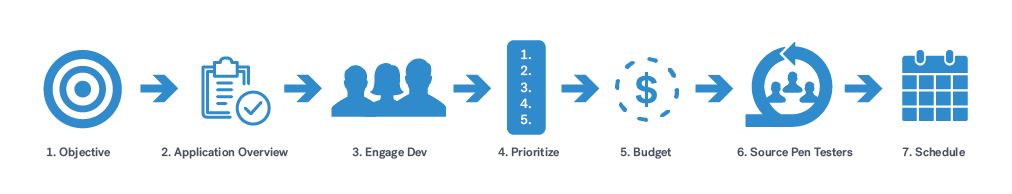
Another growing trend is the popularity of bug bounty and Pentest as as Service (PtaaS) platforms such as our own at Cobalt. These marketplaces offer an online businesses the opportunity to easily start and manage their own bug bounty program, and leverage the power of the security community.
Explore the differences between a penetration test and bug bounty program.