You’ve discovered a new vulnerability in your infrastructure. If you’re lucky, it’s something you can handle without too much red tape, but things are rarely that simple. Whether it needs to land on an engineering roadmap or it delays a product launch, remediation many times impacts the entire organization and requires buy-in from other team leads. How do you get them to prioritize it?
You need to communicate a vulnerability’s potential impact in a language that they will understand. Here are several techniques I’ve learned from shaping security at companies like Amazon, eBay, and Cobalt — each unique in its structure and business direction.
Leave the Scare Tactics Behind
Vulnerabilities are only significant as long as they pose a risk to the organization. My responsibility is to communicate these risks to stakeholders in a way that will empower them to make well-informed decisions. ‘Doom and gloom’ doesn’t take the conversation very far anymore, and it certainly won’t get others excited about leaning into new initiatives.
Instead of scaring stakeholders into agreement, I look for ways to tie security outcomes to specific business goals. Depending on the situation, I position my argument in two ways:
- By quantifying the impact of an unaddressed vulnerability. Data can help put risk into context and address unfounded assumptions.
- By demonstrating how vulnerability management enables a business objective. For example, a robust program helps speed up sales cycles with certifications like ISO 27001 or SOC 2. (Here’s a practical guide on how to get SOC 2 Type 1 certified.)
“What kind of data should I use?” you may ask. Here’s are some examples I find the most informative:
- Current vulnerabilities in your organization’s assets.
- Risk ranking based on exploit likelihood, along with its perceived business impact. You can refer to the OWASP Risk Rating Methodology or the Common Vulnerability Scoring System by FIRST.
- Real-world examples of breaches that leveraged similar or identical vulnerabilities.
- Impact of these vulnerabilities on organizations with a similar technology stack.
I aim to include facts from both internal assessments and wider industry trends. Showing that other companies are prioritizing similar weaknesses can give your recommendations that much more weight. If you don’t come prepared with real data, I can promise you you’ll be sent back to do more work.
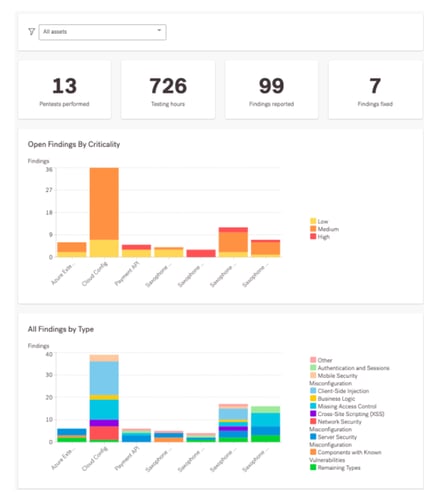
If you’re a Cobalt customer, you can use the Insights tab on our Pentest as a Service platform to visualize specific points, such as the criticality of open vulnerabilities or all findings by type. These graphs help quickly evaluate assets, identify which findings require attention for immediate remediation, and assess what additional training is required to reduce specific vulnerability types.
Find the Right Format
You can collect all the data out there and still get a passive response if your brief lacks clarity. My approach is to summarize key points in 1-2 pages. If my colleagues prefer a different format, say a slide deck, I’ll adjust accordingly. The goal is to find what lands best with the people whose buy-in you need.
As for what I cover in these documents, here are the fundamentals:
- An overview of discovered vulnerabilities, their severity and how they can impact the business.
- My remediation recommendations and a suggested timeline.
- A clear request for the resources my team needs.
You might already have frequent opportunities to communicate this information — for example, certain compliance frameworks require regular security briefings to the C-suite and board of directors.
If you don’t have these meetings already in place, I strongly recommend them. Make them regular, structured, with a clearly outlined agenda using secure board management software to collaborate more effectively. If you need to raise an urgent issue with little time for meetings, make sure that your brief inspires next steps, which you can recommend at the end of your briefing document — be it a call, a series of tickets or anything else that can kickstart remediation.
What to Do if the Answer Is “No”
No matter how well you prepare, there will be times when your leadership team decides remediation is not the company’s highest priority. As demoralizing as this can be, I have two pieces of advice:
-
Manage emotions. I take the time to first check my own emotions, and then go back to my team with the update. I aim to be their rock, explain how things stand, empathize with their frustration and disappointment, and guide the conversation to what’s the next thing we’re going to do. As long as I’m not there sulking with them, I can keep a level of morale and help them rally around how to re-address the issue.
-
Focus on what you CAN do. If the response to a high-risk vulnerability is “not now,” aim to get a commitment as to when it can be a priority. Minimize its impact as much as you can until then, for example by monitoring for suspicious activity, isolating vulnerable environments, or informing secure development to prevent its distribution along your systems.
Develop a Process That Works for Your Organization
As a security leader, it’s my job to figure out how my colleagues best respond to security risks and what we can do to enable success. While in this article I’ve tried to outline what’s worked for me, I encourage you to make adjustments that better align with your organization’s culture and processes.
If you’re interested in more practical tips from security leaders, make sure to sign up for our upcoming SecTalks virtual conference. We’ll be talking about leadership, maturing your security programs and building resilience within your teams with experts like Akamai’s CSO Andy Ellis, OneLogin’s Chief Trust and Security Officer Vanessa Pegueros, Oracle’s Senior VP and CISO David Cross, and many more seasoned industry leaders — check out the full list on our conference page.









