Navigating 2020 has taught us many valuable lessons about handling uncertainty, improving communication, and continuing business as usual during definitely-not-usual times.
As the year nears its end, we thought we’d take a moment to summarize the top lessons we’ve learned from qualitative & quantitative research, thought leadership pieces, panel discussions, and customer stories.
Lesson #1: Pentesting has changed
Earlier this year, we commissioned a study into the impact of Pentest-as-a-Service (PtaaS). Conducted by Dr. Chenxi Wang, it features in-depth interviews with five Cobalt customers. These are primarily SaaS and enterprise software vendors spanning various company sizes in both the private and public sectors.
We conducted a similar study back in 2017, exploring some of the same questions. In comparing the results, we identified some telling differences:
1. The motivation behind pentesting has changed.
Three years ago, the majority of pentest engagements were driven by compliance obligations and customer requirements. This has shifted over the last three years, with 2020 interviewees citing an internal need to make their applications and services more secure as the core driver for pentesting. Some of this is due to heightened awareness among company executives that they need to improve breach resilience across their digital environments. 2. Application security has become a shared responsibility. Where application security was once the exclusive domain of security teams, it is now increasingly a shared responsibility between security and engineering. This is because it is impossible for security teams to keep up with the speed and volume of development, and because engineering teams are simply better placed to understand the intricacies of their code.
2. Higher security demands have expanded pentesting’s scope.
In line with the shift away from exclusively compliance-focused pentesting, more organizations now pentest 100% of their applications at least annually. The interviewees also noted the importance of more frequent pentesting for business-critical assets, which in 2020 have expanded to APIs, microservices, and internal enterprise applications.
Lesson #2: Agility is critical
Teams now work much faster. Our annual “State of Pentesting” report found that 25% of organizations release software daily, and 22% release monthly. What’s more, more than half (54%) of respondents’ teams use an agile development methodology.
These stats beg the question: How can pentesting keep up?
To find an answer, we enlisted the help of renowned DevSecOps expert Larry Maccherone. In partnership with Cobalt’s Chief Strategy Officer, Caroline Wong, Larry produced a white paper on the topic.
Here are the top takeaways:
- Security teams must establish smaller, more frequent pentests as an out-of-band activity, while engineers build fast, simple testing into the CI/CD pipeline.
- Pentesting should inform secure development. In addition to highlighting individual vulnerabilities, pentest findings can show engineers which issues to watch for in future code.
- On-demand pentesting and integration with software development tools enable security teams to support engineering roadmaps and improve collaboration between the two functions.
Lesson #3: Large annual pentests are insufficient
So, two pieces of research and expertise from a DevSecOps transformation lead suggest the same thing: security teams have to cover more ground with pentesting, and make the process as agile and flexible as possible. How can that happen?
Take the example of KUBRA, a Cobalt customer that provides CX solutions for large utility, insurance, and government organizations. Focused on protecting the company’s public-facing web applications, KUBRA’s security team wanted to aim higher than just PCI compliance.
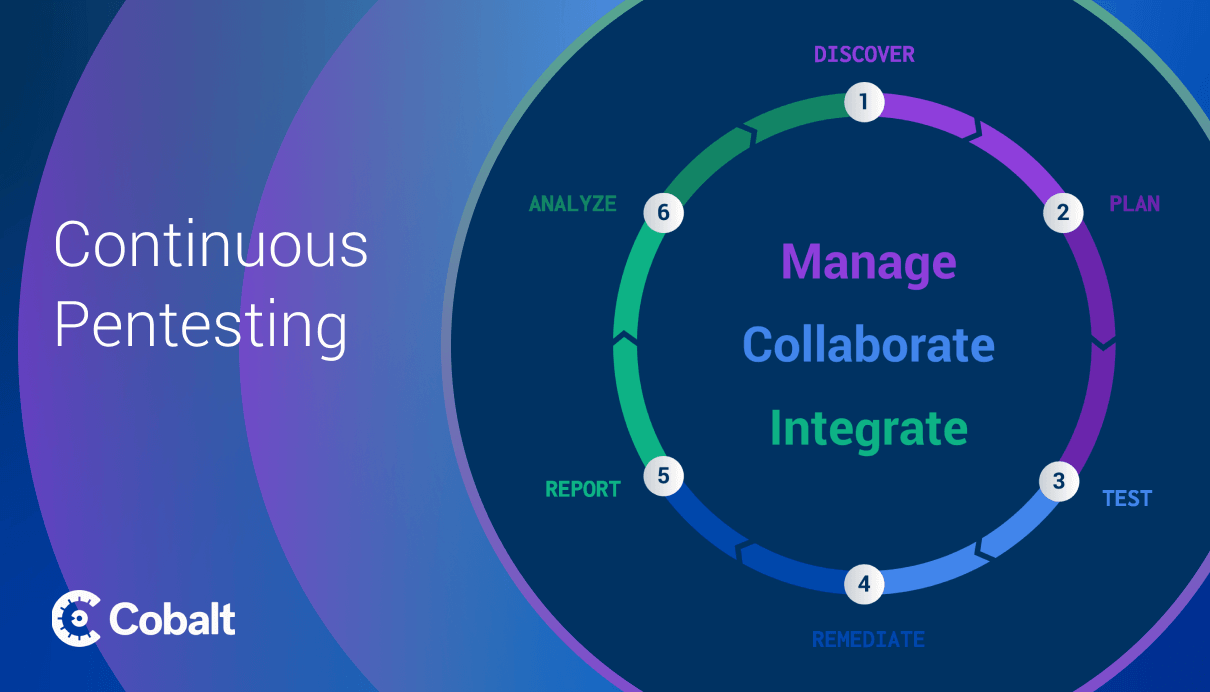
The solution: replace large annual arrangements with a continuous pentest program.
Key points include:
- What a pentest program is and how it works
- How to build one for your organization
- Which methodology to choose
- Which stakeholders to involve
- How to gain support from your executive team
- An example of a pentest program in action
Lesson #4: Engineering teams want efficiency and guidance
Up until now, we’ve explored pentesting from the security perspective… But what do engineers have to say about it?
We asked Cobalt’s VP of Engineering, Georgi Staykov, to share his insights from years spent in the field. He highlighted four challenges organizations must overcome to align pentesting with DevOps:
- Strategy. Security and engineering must both buy into a clear set of metrics and agree on how they should improve over a 1-2 year period.
- Integrations. The traditional PDF approach to pentest reporting is no longer realistic. DevOps is all about speed and automation, so pentest reporting must follow a similar approach.
- Guidance. Most engineers aren’t security experts. Security teams can add tremendous value by providing expertise and direction as needed to support secure development.
- Recurrence. As valuable as pentests are, holding a large engagement once or twice per year doesn’t provide the current security insights needed to improve product security.
Not only that, but he also proposed practical solutions to each point.
Last, but certainly not least, we wanted to highlight learnings on soft skills. If AppSec is to be a shared responsibility between security and engineering, we wanted to know how the two teams can better work together. We invited a cross-functional panel from both sides to explore the topic and their discussion was wide-ranging, covering points that included:
- Why tensions arise: security and engineering teams have different incentives — and they often clash if not managed carefully.
- What goes wrong in the real world: many organizations find themselves in a position where everybody says the right things, but nobody does them.
- How to improve collaboration: better communication is essential, and security teams can play a more consultative role for engineering teams and the business at large.
Looking Forward to 2021
We can sum up the lessons highlighted in this article into three overarching trends:
- Organizations and their customers are increasingly security-conscious.
- Organizations expect security to support business objectives — notably, faster engineering cycles.
- These trends are forcing security functions — including pentesting — to change dramatically. What was once primarily a compliance requirement has become a critical business function.
As we look forward to 2021 — hopefully, a year less affected by global events — we expect each of these trends to continue. Security teams will keep adapting their systems and processes to accommodate changing business needs. In some cases, they’ll need to radically shift their strategies to make this possible.
As your team reflects on its challenges and successes from 2020, consider how the lessons and trends highlighted here have affected your organization. And remember: Whatever happens in the next year, the ability to quickly adapt to changing needs and circumstances will undoubtedly be essential.