This blog post is part of an ongoing series in which members of the Cobalt product team provide deep dives into specific platform features.
We're excited to roll out a new Pentest Coverage Checklist feature on our PtaaS platform that is designed to give our customers transparency and confidence into the methodology followed by our pentesters.
What is the Coverage Checklist?
The Coverage Checklist is a list of checks that guides pentesters into following a baseline of security controls depending on the test’s requirements. For example, for Web, API, and Mobile assets, Cobalt follows an industry-standard, OWASP ASVS (Level 3) list. The checklist is displayed in the Cobalt platform, where customers can see each item in detail and the progress pentesters are making throughout the engagement.
For certain test environments that have a methodology but lack a defined checklist, the feature introduces custom, Cobalt-developed lists based on vendor best practices combined with the consolidated experience of Cobalt pentest architects and the pentester community. These lists cover testing checks for internal and external network assets, as well as configuration testing checks for cloud-based assets including Amazon Web Services (AWS), Google Cloud Platform (GCP), and Microsoft Azure.
The main objective of this feature is not to prescribe how a pentest should be done, but to help coordinate pentesters' efforts and to ensure baseline coverage. Typically the detailed work of the pentesters goes beyond what is covered by the Coverage Checklist.
How it works
This collaborative, baseline checklists filled out by the pentesters provides real-time transparency into the testing process. As pentesters go through the list, they mark down each complete item.
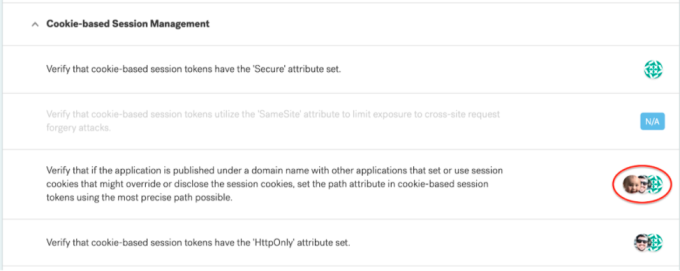
- The Avatars on the right side indicate who completed the check. The dashboard allows multiple pentesters to work on the same security control and report their progress simultaneously:
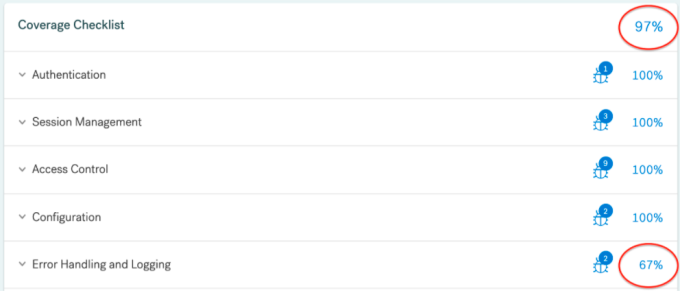
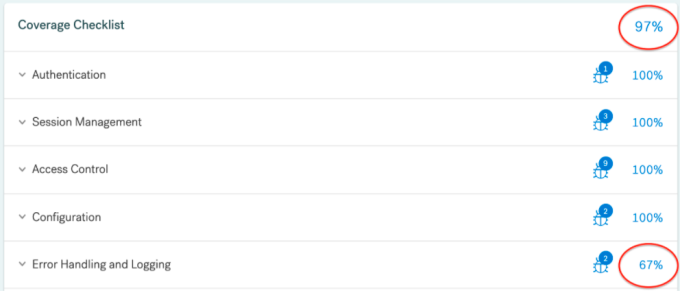
- The feature enables real-time progress tracking by displaying the status of completed checks for the entire asset or on a Category level:
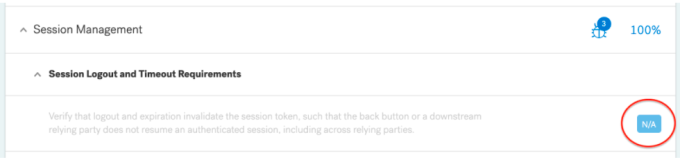
- The feature allows pentesters to mark certain verification steps, or an entire category, as Not Applicable (N/A). A check can be marked as N/A if it’s outside the planned testing scope:
- Findings identified during the pentest are categorized and reported under the relevant Coverage categories. This enables pentesters to to point out the security controls that need to be fixed, but also to capture the security controls that have been scrutinized and have passed the tests successfully:
As we continue to be a leader in PtaaS, we are always looking for ways to ensure Cobalt is the most innovative solution for DevOps-driven software companies that want to implement security across the development lifecycle and optimize application security processes.
Curious to learn more? Schedule time with one of our security experts to see Cobalt in action or view the platform with an on-demand PtaaS demo!