All organizations that have undergone a pentest understand the importance of a pentest report. Pentest (PT) reports are an important artifact that are usually shared with various stakeholders. Depending on the type of stakeholders, the information on the report should change. E.g. If pentest reports are shared with engineering stakeholders to collaborate on fixing the vulnerabilities, then the PT report needs to be in-depth with detailed vulnerability information.
If PT reports are shared with compliance or internal audit teams, vulnerability information needs to be summarized to understand the overall risk to the organization and whether it falls within the security policy of the organization. If PT reports are shared with prospects or customers, they are high-level, summarizing the risks of the asset and any corrective actions that have been already taken to alleviate concerns of prospects/customers.
Cobalt’s PtaaS platform already offers 4 different types of PT reports to cater to the needs of various stakeholders. However, there is additional need in the market to be able to further fine-tune those PT reports when presenting it to stakeholders, especially external ones.
Introducing Cobalt’s new configurable PT report that enables users to adjust layout to a very granular level while still preserving the integrity of the original information. Thereby, it preserves the element of trust in the report while offering to cater to different stakeholders inside and outside the organization.
How does it work?
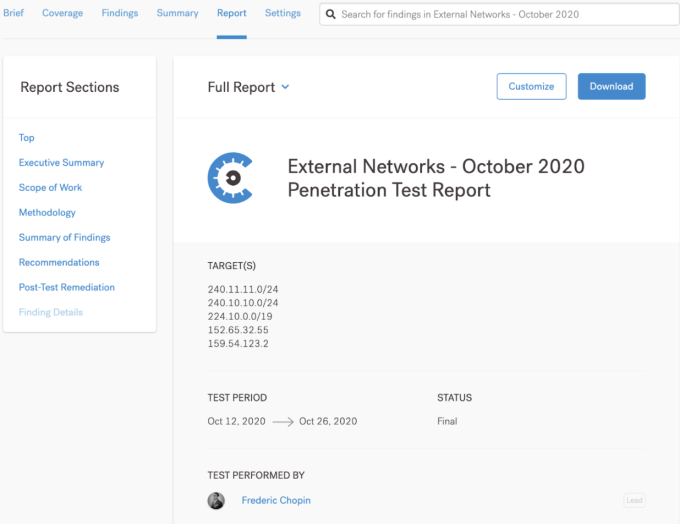
Once a pentest is complete and the report is final, it becomes visible and accessible to customers through Cobalt’s platform. There are four types of pentest reports:
- Customer Letter
- Attestation Letter
- Full Report
- Full Report + Finding Details
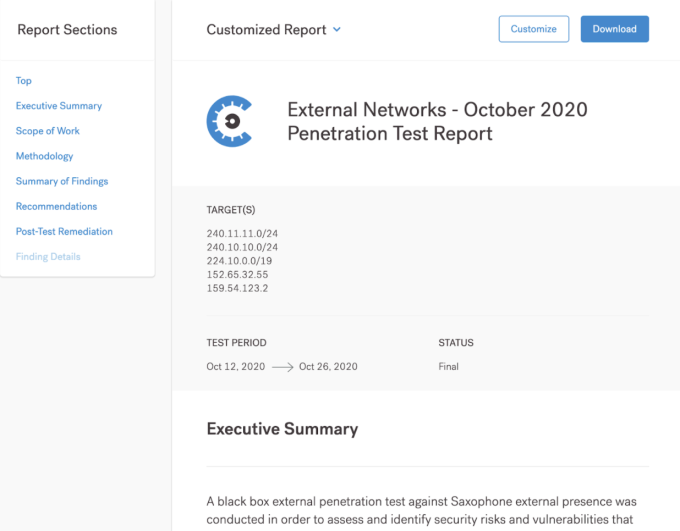
In addition, users can customize any of the above four and save a copy of it. By default, “Full Report” is visible to users when they go to the report section of the platform. On the left side in the “Report Sections” users can see various components of enclosed content. Some options are grayed out depending on whether they are available. If users decide to customize the selected report, they can simply click on the “Customize” button.
After clicking the “Customize” button, the same report will appear in a modal with the ability to include or exclude sections. Inclusion is shown by the “open eye” icon.
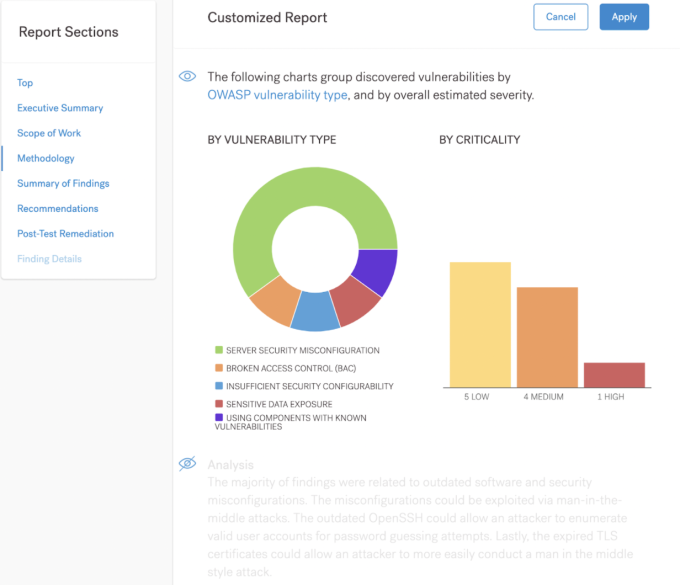
Users can exclude any identified sections of the report from the final version by simply clicking the “open eye” control. Once clicked, it will fade those sections of the report to visually indicate that they are not included in the report.
After going through the report and including/excluding appropriate sections, users can “Apply” those changes. They can then download the customized PT report in PDF format.
With this level of customization, customers will be able to control pentest report information shared with their stakeholders at a granular level and be able to accomplish the objectives with various stakeholders.
As we continue to lead PtaaS, we are always looking for ways to ensure Cobalt is the most innovative solution for DevOps-driven software companies that want to implement security across the development lifecycle and optimize application security processes. Check out an on-demand PtaaS demo today!